Netherlands Data Breach: 7.3 Million Car Owners’ Data Exposed
RDC Data Breach - When Car Data Became a Goldmine for Hackers
In early 2021, the Netherlands faced one of its most consequential data breaches when RDC B.V., a company providing digital platforms for car dealers and garages, confirmed that personal and vehicle data from 7.3 million Dutch car owners had been leaked online. The incident, later dubbed the biggest automotive data breach in Dutch history, offers a sharp lesson in how the digital transformation of the mobility sector has outpaced its cybersecurity maturity.
In early 2021, the Netherlands faced one of its most consequential data breaches when RDC B.V., a company providing digital platforms for car dealers and garages, confirmed that personal and vehicle data from 7.3 million Dutch car owners had been leaked online. The incident, later dubbed the biggest automotive data breach in Dutch history, offers a sharp lesson in how the digital transformation of the mobility sector has outpaced its cybersecurity maturity.
Read more on NL-TIMES
What Happened
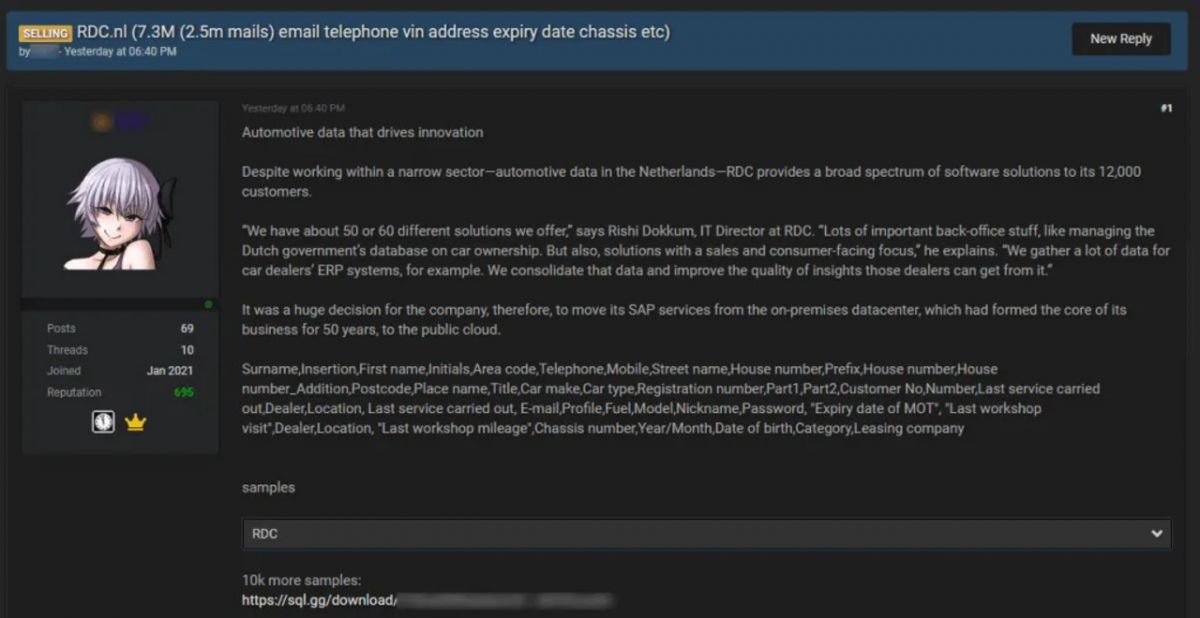
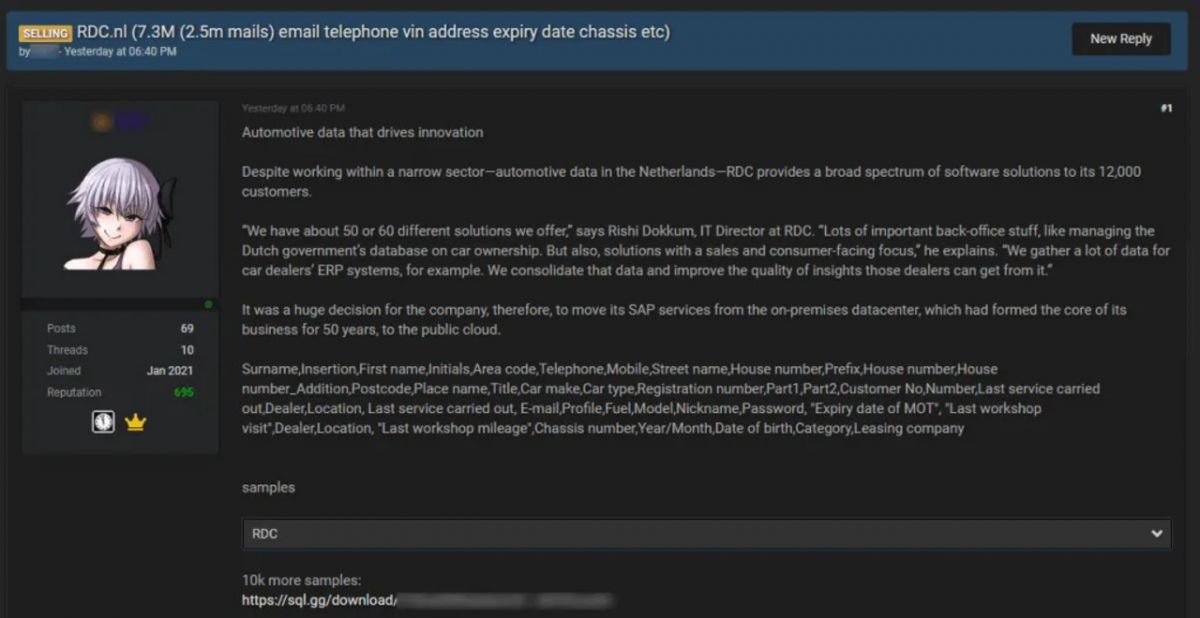
RDC operates at the heart of the Dutch automotive ecosystem, connecting garages, car dealerships, and insurers through a network of cloud-based services. In March 2021, researchers on a dark-web forum noticed a database being sold for cryptocurrency - the listing claimed to include “full owner information and license-plate data of all cars registered in the Netherlands.”
Soon after, cybersecurity reporters traced the sample records back to RDC. Dutch tech platform TWEAKERS NIEUWS confirmed that portions of the leaked data were being traded on criminal forums.The exposed dataset contained names, email addresses, phone numbers, home addresses, vehicle license plates, VIN numbers, and car models - a combination of personal and technical identifiers that together form a complete profile of each driver.
Within days, the Dutch data protection authority (Autoriteit Persoonsgegevens) launched an investigation, and RDC confirmed that an unauthorized third party had accessed customer databases through one of its web applications.
Technical Breakdown
Public technical disclosures remain limited, but forensic analysis points to a web application vulnerability - possibly an outdated API endpoint that failed to sanitize input or authenticate queries. This allowed attackers to perform enumeration attacks, scraping massive volumes of records before detection.
Evidence suggests the breach occurred months before it was publicly disclosed. Logs indicated large, automated data extractions, likely performed through scripts that mimicked legitimate dealer queries.
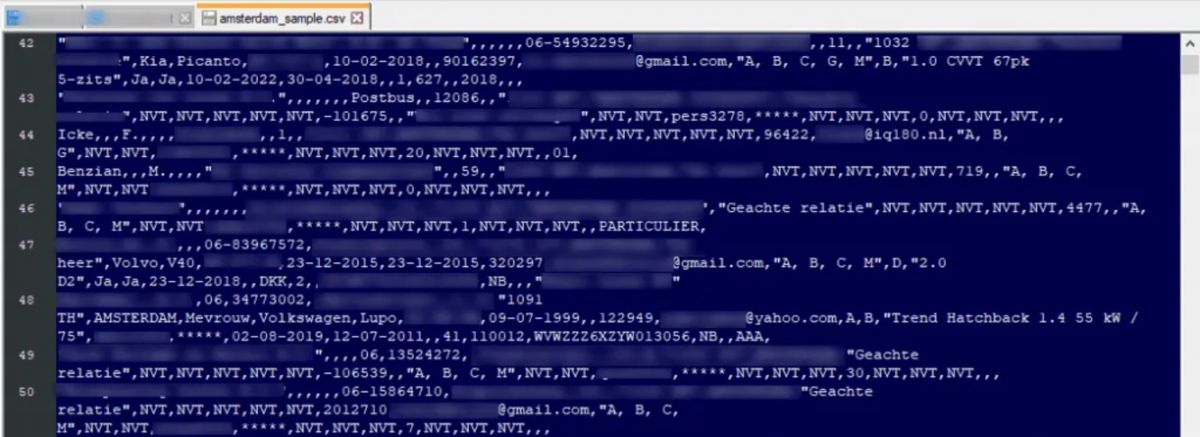
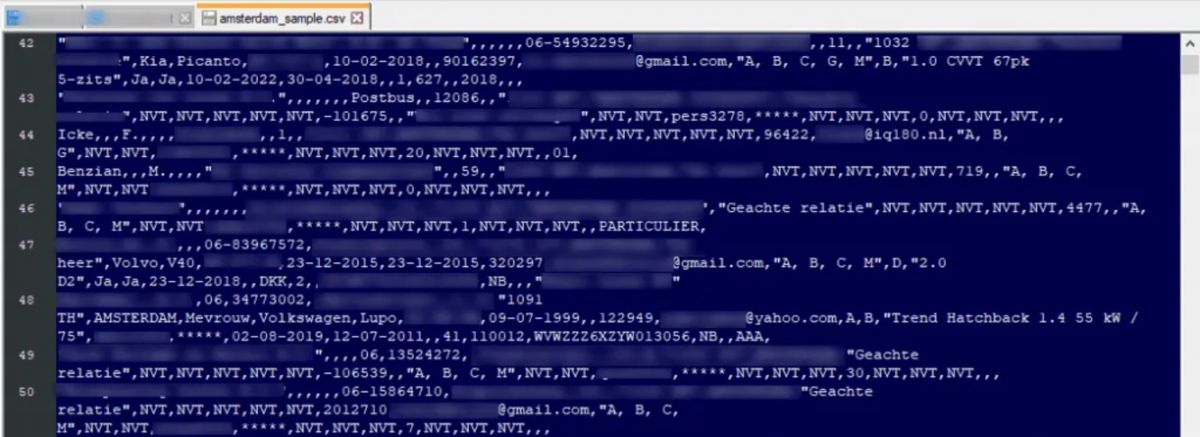
Once the dataset was exfiltrated, it appeared for sale on several dark-web marketplaces. Security analysts found samples containing realistic combinations of personal data and license-plate numbers, confirming its authenticity.
The breach demonstrates a recurring weakness: legacy infrastructure built for convenience, not security. Many automotive IT systems were designed for data sharing within trusted business networks - not for exposure to the internet or constant probing by threat actors.
The Dark Web Aftermath
Following the leak, the stolen data spread rapidly. Investigators observed multiple resellers reposting parts of the database, often advertising it to criminal groups specializing in fraud, phishing, and identity theft.
One common scam that emerged soon after involved fraudulent car-tax refund emails that referenced the victim’s actual vehicle model and license plate - details lifted directly from the RDC dump. This blending of authentic-looking personal data with social-engineering tactics made the campaigns alarmingly effective.
The Dutch National Cyber Security Centre (NCSC-NL) later cited the RDC case as a textbook example of how information from sector-specific systems can amplify general cybercrime once it enters the underground economy.
Regulatory and Legal Fallout
Under the EU GDPR, data controllers are obligated to notify both authorities and affected individuals within 72 hours of confirming a breach. RDC complied, sending out tens of thousands of email notifications and coordinating with regulators.
However, the event raised critical questions about supply-chain accountability. Car dealerships using RDC’s systems were technically separate businesses but relied on RDC to safeguard customer data. When RDC failed, every connected dealer faced reputational and legal exposure.
Dutch IT publication at COMPUTABLE has covered related investigations, stressing how vulnerabilities in interconnected systems can escalate into national exposure.
The Autoriteit Persoonsgegevens opened a formal inquiry, citing potential violations of Article 32 (GDPR - Security of Processing) and Article 33 (Notification of a Personal Data Breach). While the final penalties were never made public, the reputational damage was substantial, and RDC reportedly overhauled its cloud architecture afterward.
Lessons Learned for the Automotive Sector
Data Minimization and Encryption: Car service platforms often collect more data than necessary. Encrypting identifiers like VINs and license plates - even at rest - can limit the impact of a breach.
Zero-Trust Integration: API endpoints should never assume trust merely because a request comes from a known dealer system. Strong authentication and per-partner encryption keys are essential.
Continuous Monitoring: Automotive service ecosystems require centralized logging and anomaly detection to spot large-scale data extraction early.
Dark-Web Intelligence: Monitoring underground forums can provide early warnings that stolen data is circulating.
Shared Responsibility: Dealers, insurers, and service providers must align cybersecurity obligations contractually - it’s not enough to rely on the main IT vendor.
Broader European Implications
The RDC incident fits a growing European trend: data breaches shifting from financial to operational industries. Energy, logistics, and automotive sectors are all collecting personal data at scale, but many still lack mature cyber-risk management.
According to CYBERLANDS, the breach is among the most impactful security incidents recorded in the Netherlands over the past years.
The European Union’s NIS 2 Directive, coming into force in 2025, expands mandatory security and incident-reporting requirements to more sectors - including transport and digital service providers. RDC’s experience demonstrates why: a breach in a “non-critical” sector can have national-level consequences.
For the Netherlands, where car ownership data intersects with government road-tax systems and insurance databases, the case became an argument for public-private cyber resilience programs.
Conclusion - Protecting Mobility in a Data-Driven Era
The RDC data breach was not a sophisticated state-sponsored attack. It was a preventable systems failure - yet it exposed millions and revealed how valuable everyday mobility data has become.
For European car dealers, insurers, and service platforms, the message is clear: the road to digital transformation must include a strong cybersecurity foundation. Cars may run on fuel or electricity, but the mobility industry now runs on data - and that data has to be secured as carefully as the vehicles themselves.
What Happened
RDC operates at the heart of the Dutch automotive ecosystem, connecting garages, car dealerships, and insurers through a network of cloud-based services. In March 2021, researchers on a dark-web forum noticed a database being sold for cryptocurrency - the listing claimed to include “full owner information and license-plate data of all cars registered in the Netherlands.”
Soon after, cybersecurity reporters traced the sample records back to RDC. Dutch tech platform TWEAKERS NIEUWS confirmed that portions of the leaked data were being traded on criminal forums.The exposed dataset contained names, email addresses, phone numbers, home addresses, vehicle license plates, VIN numbers, and car models - a combination of personal and technical identifiers that together form a complete profile of each driver.
Within days, the Dutch data protection authority (Autoriteit Persoonsgegevens) launched an investigation, and RDC confirmed that an unauthorized third party had accessed customer databases through one of its web applications.
Why This Breach Matters
Most people don’t think of a car as a digital privacy risk. Yet, as vehicles become connected - and as service providers aggregate vast databases about owners, mileage, insurance, and maintenance - automotive data has become as valuable as health or banking information.
The RDC case exposed how a single vulnerable link in the supply chain can compromise millions of individuals. Unlike traditional ransomware attacks that demand payment, this was data monetization via the dark web: stolen information packaged and resold for targeted scams, phishing, or even physical crimes like vehicle theft.
Most people don’t think of a car as a digital privacy risk. Yet, as vehicles become connected - and as service providers aggregate vast databases about owners, mileage, insurance, and maintenance - automotive data has become as valuable as health or banking information.
The RDC case exposed how a single vulnerable link in the supply chain can compromise millions of individuals. Unlike traditional ransomware attacks that demand payment, this was data monetization via the dark web: stolen information packaged and resold for targeted scams, phishing, or even physical crimes like vehicle theft.
Security researchers at KNOWBE4 later analyzed how the leaked datasets were being repurposed for phishing and fraud campaigns.
From a national perspective, it was a wake-up call: the Netherlands’ highly digitalized mobility infrastructure depends on data trust. When that trust is lost, the impact ripples far beyond one company.
From a national perspective, it was a wake-up call: the Netherlands’ highly digitalized mobility infrastructure depends on data trust. When that trust is lost, the impact ripples far beyond one company.
Technical Breakdown
Public technical disclosures remain limited, but forensic analysis points to a web application vulnerability - possibly an outdated API endpoint that failed to sanitize input or authenticate queries. This allowed attackers to perform enumeration attacks, scraping massive volumes of records before detection.
Evidence suggests the breach occurred months before it was publicly disclosed. Logs indicated large, automated data extractions, likely performed through scripts that mimicked legitimate dealer queries.
Once the dataset was exfiltrated, it appeared for sale on several dark-web marketplaces. Security analysts found samples containing realistic combinations of personal data and license-plate numbers, confirming its authenticity.
The breach demonstrates a recurring weakness: legacy infrastructure built for convenience, not security. Many automotive IT systems were designed for data sharing within trusted business networks - not for exposure to the internet or constant probing by threat actors.
The Dark Web Aftermath
Following the leak, the stolen data spread rapidly. Investigators observed multiple resellers reposting parts of the database, often advertising it to criminal groups specializing in fraud, phishing, and identity theft.
One common scam that emerged soon after involved fraudulent car-tax refund emails that referenced the victim’s actual vehicle model and license plate - details lifted directly from the RDC dump. This blending of authentic-looking personal data with social-engineering tactics made the campaigns alarmingly effective.
The Dutch National Cyber Security Centre (NCSC-NL) later cited the RDC case as a textbook example of how information from sector-specific systems can amplify general cybercrime once it enters the underground economy.
Regulatory and Legal Fallout
Under the EU GDPR, data controllers are obligated to notify both authorities and affected individuals within 72 hours of confirming a breach. RDC complied, sending out tens of thousands of email notifications and coordinating with regulators.
However, the event raised critical questions about supply-chain accountability. Car dealerships using RDC’s systems were technically separate businesses but relied on RDC to safeguard customer data. When RDC failed, every connected dealer faced reputational and legal exposure.
Dutch IT publication at COMPUTABLE has covered related investigations, stressing how vulnerabilities in interconnected systems can escalate into national exposure.
The Autoriteit Persoonsgegevens opened a formal inquiry, citing potential violations of Article 32 (GDPR - Security of Processing) and Article 33 (Notification of a Personal Data Breach). While the final penalties were never made public, the reputational damage was substantial, and RDC reportedly overhauled its cloud architecture afterward.
Lessons Learned for the Automotive Sector
Data Minimization and Encryption: Car service platforms often collect more data than necessary. Encrypting identifiers like VINs and license plates - even at rest - can limit the impact of a breach.
Zero-Trust Integration: API endpoints should never assume trust merely because a request comes from a known dealer system. Strong authentication and per-partner encryption keys are essential.
Continuous Monitoring: Automotive service ecosystems require centralized logging and anomaly detection to spot large-scale data extraction early.
Dark-Web Intelligence: Monitoring underground forums can provide early warnings that stolen data is circulating.
Shared Responsibility: Dealers, insurers, and service providers must align cybersecurity obligations contractually - it’s not enough to rely on the main IT vendor.
Broader European Implications
The RDC incident fits a growing European trend: data breaches shifting from financial to operational industries. Energy, logistics, and automotive sectors are all collecting personal data at scale, but many still lack mature cyber-risk management.
According to CYBERLANDS, the breach is among the most impactful security incidents recorded in the Netherlands over the past years.
The European Union’s NIS 2 Directive, coming into force in 2025, expands mandatory security and incident-reporting requirements to more sectors - including transport and digital service providers. RDC’s experience demonstrates why: a breach in a “non-critical” sector can have national-level consequences.
For the Netherlands, where car ownership data intersects with government road-tax systems and insurance databases, the case became an argument for public-private cyber resilience programs.
Conclusion - Protecting Mobility in a Data-Driven Era
The RDC data breach was not a sophisticated state-sponsored attack. It was a preventable systems failure - yet it exposed millions and revealed how valuable everyday mobility data has become.
For European car dealers, insurers, and service platforms, the message is clear: the road to digital transformation must include a strong cybersecurity foundation. Cars may run on fuel or electricity, but the mobility industry now runs on data - and that data has to be secured as carefully as the vehicles themselves.